Address medical data security with HITRUST CSF certification
Business Challenge
Businesses that create, access, store or exchange protected health information (PHI) must adhere to strict data standards and regulations, including the Health Information Trust Alliance (HITRUST™) Common Security Framework (CSF). The HITRUST CSF controls help businesses reduce the risk of a data breach, which can result in costly penalties, legal actions and serious reputational damage.
HITRUST CSF consists of controls pulled from a number of globally recognized security frameworks and regulations — including the Health Insurance Portability and Accountability Act (HIPAA), the Health Information Technology for Economic and Clinical Health Act (HITECH), the Payment Card Industry Data Security Standard (PCI DSS), Control Objectives for Information and Related Technologies® (COBIT®) and recommendations from the National Institute of Standards and Technology (NIST) and the International Organization for Standardization (ISO).
HITRUST CSF-Certified Dedicated Environments
Our HITRUST CSF certification helps ensure that your dedicated hosting environment exceeds the healthcare industry’s complex data privacy and security regulations. We provide our HITRUST CSF-certified dedicated hosting environment at no additional cost, so you can start reducing costs and driving efficiency.

Use Cases
Most healthcare organizations, including health insurance companies, hospitals, medical practices and SaaS providers require a HITRUST CSF certified infrastructure. Discover how our HITRUST CSF certification can help you keep your IT infrastructure compliant, while you move your workloads to the cloud.

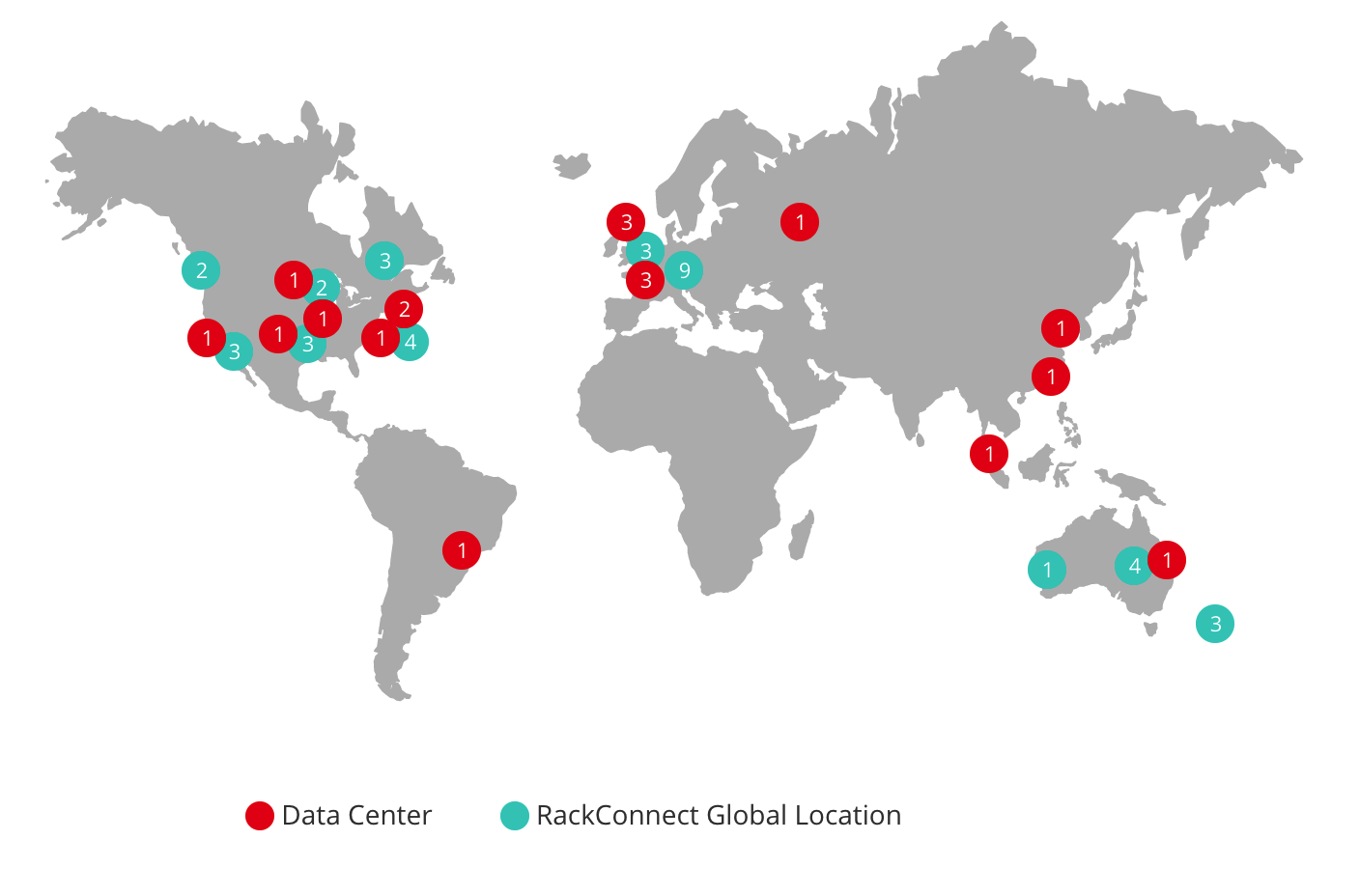
Our HITRUST CSF certification applies to all of our data centers around the world — including our dedicated servers, private cloud, databases, networking and storage solutions.
Controls & Governance
Our dedicated hosting environment has been validated against all 300+ HITRUST requirements — across 19 different security categories— to provide comprehensive IT protection for sensitive information.
| Consideration' | HITRUST | ISO | NIST | PCI | COBIT | HIPAA |
| Comprehensive - General Security | Partial Offering | |||||
| Risk-Based (rather than compliance-based) | Partial Offering | Partial Offering | ||||
| Supported and Maintained | ||||||
| Audit or Assessment Guidelines | ||||||
| Certifiable | ||||||
| Open and Transparent Update Process | ||||||
| Consistency and Accuracy (in assessment/evaluation) | Partial Offering | Partial Offering | Partial Offering | |||
| Support for Third-Party Assurance | ||||||
| Prescriptive | Partial Offering | Partial Offering | ||||
| Assess Once and Report Many | Partial Offering | Partial Offering | ||||
| Vetted by Healthcare and Industry Experts | ISO 27799 and NIST 800-66 both subject to comment period prior to release | ISO 27799 and NIST 800-66 both subject to comment period prior to release | ||||
| Practical and Scalable | ||||||
| Comprehensive - Regulatory, Statutory and Business Requirements |
Ready to Start the Conversation?
We’re experts on your side, doing what it takes to get the job done right — from the first consultation to your daily operations.
