10 Reasons Your Cybersecurity Strategy Needs a Regular Checkup [Infographic]
davidneuman
![10 Reasons Your Cybersecurity Strategy Needs a Regular Checkup [Infographic]](/sites/default/files/article-images/blog_335.jpg)

Recent Posts
When Azure Architecture Outruns the Operating Model
May 12th, 2026
Four Barriers Limiting Healthcare Cloud Efficiency
May 11th, 2026
Related Posts
Cloud Insights
Building a Secure and Resilient Healthcare Cloud for Operational Readiness
May 21st, 2026
AI Insights
AI Is Forcing Infrastructure, Security and Governance to Converge
May 18th, 2026
AI Insights
How AI Agent Sprawl Impacts Cost and Governance Across the Bank
May 14th, 2026
Cloud Insights
When Azure Architecture Outruns the Operating Model
May 12th, 2026
Cloud Insights
Four Barriers Limiting Healthcare Cloud Efficiency
May 11th, 2026
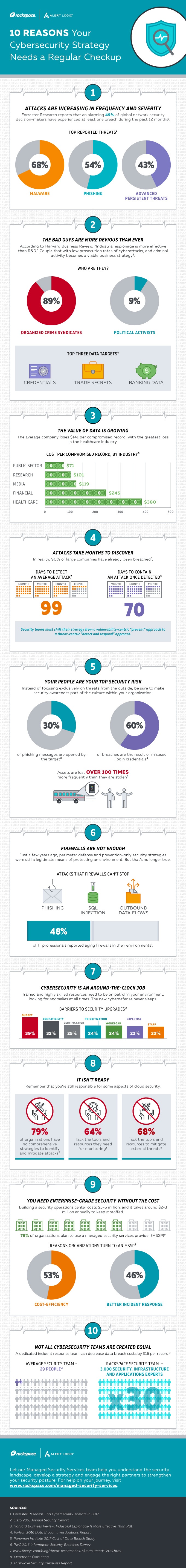
In today's cybersecurity landscape, your security strategy needs constant attention. Check out this infographic for tips on how to get started,
When was the last time you assessed your cybersecurity strategy? Given today's ever-changing security landscape, it's probably been too long.
In this world of constant cyber threats, you can’t afford to be complacent. This is especially true when security complacency is precisely what the bad guys look for when assessing a target.
With that in mind, download our new ebook, Managed Security Service Providers For Dummies, and check out the following infographic to discover why your cybersecurity strategy may be in need of a fresh look.
Learn more in our new ebook, Managed Security Service Providers For Dummies, designed to help businesses journey from the do-it-yourself model to leveraging a managed service provider. It includes best practices for adjusting your security strategy, guidance for optimizing your resources and more. It’s a great first step toward establishing a strong security posture in the cloud. Download it here!
Tags:




