
Recent Posts
Skalierung von KI-Lösungen in der Private Cloud, vom PoC zur Produktion
Dezember 4th, 2025
Ein umfassender Leitfaden zur PVC-Implementierung
November 11th, 2025
KI-gestützte Datenerpressung: Eine neue Ära der Ransomware
September 2nd, 2025
Related Posts
AI Insights
Skalierung von KI-Lösungen in der Private Cloud, vom PoC zur Produktion
Dezember 4th, 2025
AI Insights
Ein umfassender Leitfaden zur PVC-Implementierung
November 11th, 2025
AI Insights
KI-gestützte Datenerpressung: Eine neue Ära der Ransomware
September 2nd, 2025
AI Insights
Der erste Schritt der KI ist die Datenbereitstellung. Wie befähigte Nutzer und Datenplattformen die nächste Stufe der generativen KI prägen
August 28th, 2025
Cloud Insights
Rackspace AI Security Engine stärkt Cyber-Abwehr mit adaptiver Intelligenz
August 20th, 2025
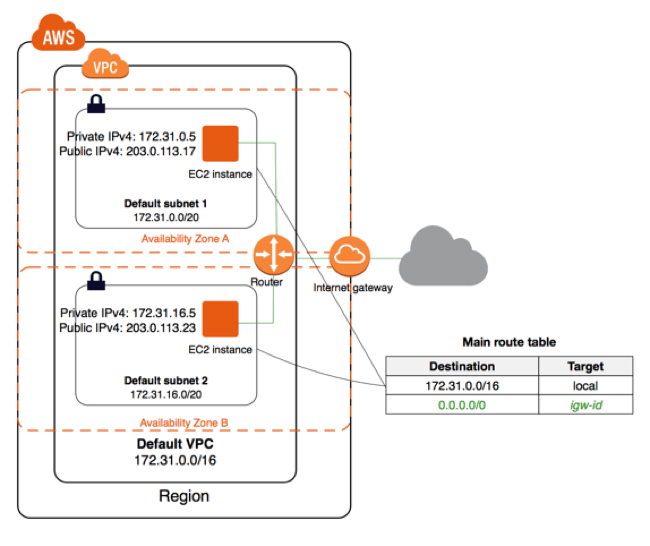
Eine Virtual Private Cloud ist ein logisch isoliertes virtuelles Netzwerk, das sich über eine ganze AWS-Region erstreckt und in dem Ihre EC2-Instanzen gestartet werden.
In meinem früheren Blogbeitrag habe ich die Grundlagen der AWS Global Infrastructure erläutert. Das Verständnis dieser Konzepte ist grundlegend für das Verständnis der AWS Virtual Private Cloud (VPC) und wie sie erweiterte Netzwerkfunktionen für Ihre AWS-Ressourcen ermöglicht. Eine VPC ist ein logisch isoliertes virtuelles Netzwerk, das sich über eine ganze AWS-Region erstreckt und in dem Ihre EC2-Instances gestartet werden. Bei einer VPC geht es in erster Linie darum, die folgenden Funktionen zu ermöglichen:
- Isolierung Ihrer AWS-Ressourcen von anderen Konten
- Routing des Netzwerkverkehrs zu und von Ihren Instanzen
- Schutz Ihrer Instanzen vor Eindringlingen in das Netzwerk
Es gibt sechs Kernkomponenten, die grundlegend für eine VPC sind und von einem Benutzer oder von AWS als Teil einer Standard-VPC erstellt werden. Diese Komponenten sind:
- VPC CIDR-Block
- Teilnetz
- Gateways
- Routen-Tabelle
- Netzwerk-Zugangskontrolllisten (ACLs)
- Sicherheitsgruppen
Jedes AWS-Konto, das nach dem 4. Dezember 2013 erstellt wurde, unterstützt VPCs und diesen Konten wird in jeder AWS-Region eine Standard-VPC zugewiesen. Diese Standard-VPCs sollen es AWS-Benutzern erleichtern, Netzwerke für ihre EC2-Instances einzurichten. Im weiteren Verlauf dieses Beitrags werde ich Ihnen zeigen, wie eine Standard-VPC in der AWS-Konsole aussieht und wichtige Standardeinstellungen hervorheben. Sie beginnen mit dem "VPC-Dashboard" in Ihrer AWS-Konsole, das einen Gesamtüberblick über die Komponenten bietet, die als Teil Ihres VPC-Footprints verfügbar sind. Beachten Sie, dass die oben genannten Basiskomponenten bereits als Teil der Standard-VPC bereitgestellt werden, die jedem AWS-Konto für jede Region zugewiesen wird. 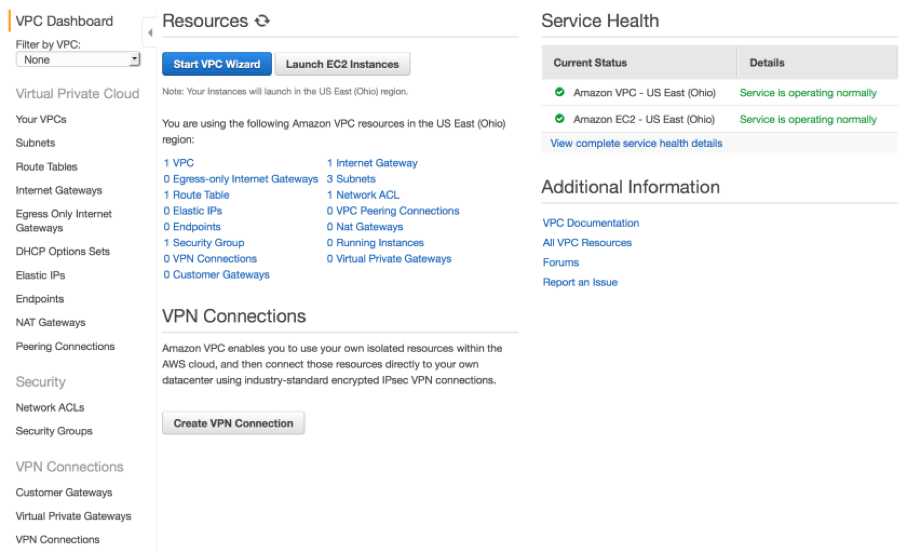
VPC CIDR-Block
Wählen Sie in der linken Seitenleiste "Ihre VPCs" aus. Im Dashboard werden alle Ihre VPCs in einer bestimmten AWS-Region angezeigt, einschließlich der Standard-VPC. Eine Region kann nur eine Standard-VPC haben. Obwohl Sie bis zu fünf VPCs in einer Region haben können, kann nur die erste VPC, die AWS für Sie erstellt, die Standard-VPC sein.  Jeder VPC ist mit einem IP-Adressbereich verbunden, der Teil eines CIDR-Blocks (Classless Inter-Domain Routing) ist, der für die Zuweisung privater IP-Adressen an EC2-Instances verwendet wird. AWS empfiehlt, dass VPCs private Bereiche verwenden, die in RFC 1918definiert sind. Diese privaten Bereiche sind von der Internet Assigned Numbers Authority (IANA) reserviert und können nicht an das Internet weitergeleitet werden. Einem VPC können je nach Bedarf unterschiedlich große Bereiche mit unterschiedlichen Zuweisungen von IP-Adressen zugewiesen werden. Alle Standard-VPCs werden mit einem IPv4-CIDR-Block mit einem 172.31.0.0/16-Adressbereich verbunden. Damit erhalten Sie 65.536 mögliche IP-Adressen, abzüglich einiger reservierter AWS-Adressen. VPCs können mit kleineren CIDR-Blöcken erstellt werden, z. B. mit /20, was 4091 mögliche Adressen ergeben würde.
Jeder VPC ist mit einem IP-Adressbereich verbunden, der Teil eines CIDR-Blocks (Classless Inter-Domain Routing) ist, der für die Zuweisung privater IP-Adressen an EC2-Instances verwendet wird. AWS empfiehlt, dass VPCs private Bereiche verwenden, die in RFC 1918definiert sind. Diese privaten Bereiche sind von der Internet Assigned Numbers Authority (IANA) reserviert und können nicht an das Internet weitergeleitet werden. Einem VPC können je nach Bedarf unterschiedlich große Bereiche mit unterschiedlichen Zuweisungen von IP-Adressen zugewiesen werden. Alle Standard-VPCs werden mit einem IPv4-CIDR-Block mit einem 172.31.0.0/16-Adressbereich verbunden. Damit erhalten Sie 65.536 mögliche IP-Adressen, abzüglich einiger reservierter AWS-Adressen. VPCs können mit kleineren CIDR-Blöcken erstellt werden, z. B. mit /20, was 4091 mögliche Adressen ergeben würde.
Teilnetz
Wenn Sie dann zum Bildschirm "Subnets" gehen, werden Sie sehen, dass Ihrer Standard-VPC bereits mehrere Standard-Subnetze zugewiesen wurden, ein Subnetz für jede Verfügbarkeitszone. 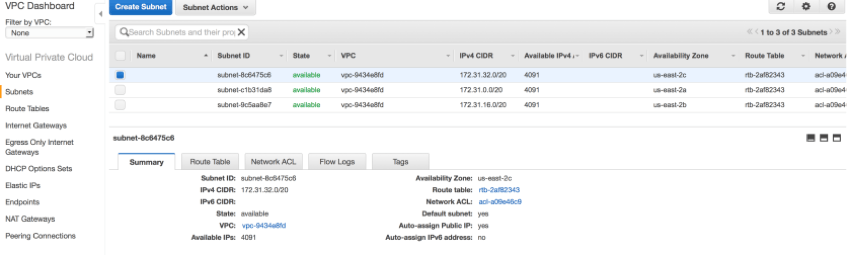 Ein Subnetz ist immer mit einer einzigen Verfügbarkeitszone verbunden und kann sich nicht über mehrere Zonen erstrecken. Eine Verfügbarkeitszone kann jedoch mehrere Subnetze beherbergen. Jedes Subnetz in einem VPC ist mit einem IPv4-CIDR-Block verbunden, der eine Teilmenge des /16-CIDR-Blocks seines VPCs ist. In einer Standard-VPC ist jedes Standard-Subnetz einem /20-CIDR-Block-Adressbereich zugeordnet, der 4091 mögliche IP-Adressen abzüglich der fünf von AWS stets reservierten Adressen umfasst. Beachten Sie, dass zwei Subnetze keine überlappenden Adressbereiche haben können. Wenn Sie eine EC2-Instanz in einer Standard-VPC starten, ohne ein bestimmtes Subnetz anzugeben, wird sie automatisch in einem der Standardsubnetze gestartet. Jede Instanz in einem Standard-Subnetz erhält eine private IP-Adresse aus dem mit diesem Subnetz verbundenen Adresspool und einen privaten DNS-Hostnamen. In einem Standard-Subnetz erhält eine Instanz auch eine öffentliche IP-Adresse aus dem AWS-eigenen Adresspool sowie einen öffentlichen DNS-Hostnamen, was den Internetzugang für Ihre Instanzen erleichtert.
Ein Subnetz ist immer mit einer einzigen Verfügbarkeitszone verbunden und kann sich nicht über mehrere Zonen erstrecken. Eine Verfügbarkeitszone kann jedoch mehrere Subnetze beherbergen. Jedes Subnetz in einem VPC ist mit einem IPv4-CIDR-Block verbunden, der eine Teilmenge des /16-CIDR-Blocks seines VPCs ist. In einer Standard-VPC ist jedes Standard-Subnetz einem /20-CIDR-Block-Adressbereich zugeordnet, der 4091 mögliche IP-Adressen abzüglich der fünf von AWS stets reservierten Adressen umfasst. Beachten Sie, dass zwei Subnetze keine überlappenden Adressbereiche haben können. Wenn Sie eine EC2-Instanz in einer Standard-VPC starten, ohne ein bestimmtes Subnetz anzugeben, wird sie automatisch in einem der Standardsubnetze gestartet. Jede Instanz in einem Standard-Subnetz erhält eine private IP-Adresse aus dem mit diesem Subnetz verbundenen Adresspool und einen privaten DNS-Hostnamen. In einem Standard-Subnetz erhält eine Instanz auch eine öffentliche IP-Adresse aus dem AWS-eigenen Adresspool sowie einen öffentlichen DNS-Hostnamen, was den Internetzugang für Ihre Instanzen erleichtert. 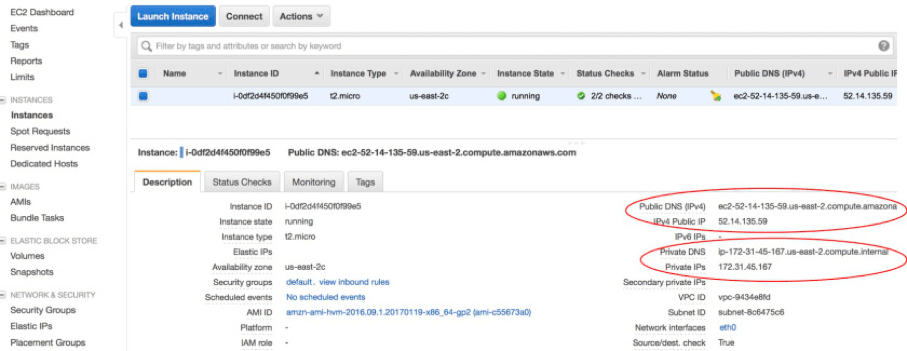
Gateways
Häufig benötigen Ihre EC2-Instanzen über Gateways eine Verbindung außerhalb von AWS zum Internet oder zum Unternehmensnetzwerk eines Benutzers. Für die Kommunikation mit dem Internet muss ein VPC mit einem Internet-Gateway verbunden sein. Ein Internet-Gateway ist ein vollständig verwalteter AWS-Service, der eine bidirektionale Übersetzung der Quell- und Zielnetzwerkadressen für Ihre EC2-Instances durchführt. Optional kann ein VPC ein virtuelles privates Gateway verwenden, um Instanzen über VPN- oder Direktverbindungen sicheren Zugang zum Unternehmensnetz eines Benutzers zu gewähren. Instanzen in einem Subnetz können über ein NAT-Gateway auch nur einen ausgehenden Internetzugang erhalten. Ein Subnetz, das seinen Instanzen eine Route zu einem Internet-Gateway bietet, gilt als öffentliches Subnetz. Ein privates Subnetz kann sich in einer VPC mit einem angeschlossenen Internet-Gateway befinden, verfügt aber nicht über eine Route zu diesem Gateway. In einer Standard-VPC sind alle Standard-Subnetze öffentliche Subnetze und verfügen über eine Route zu einem Standard-Gateway. 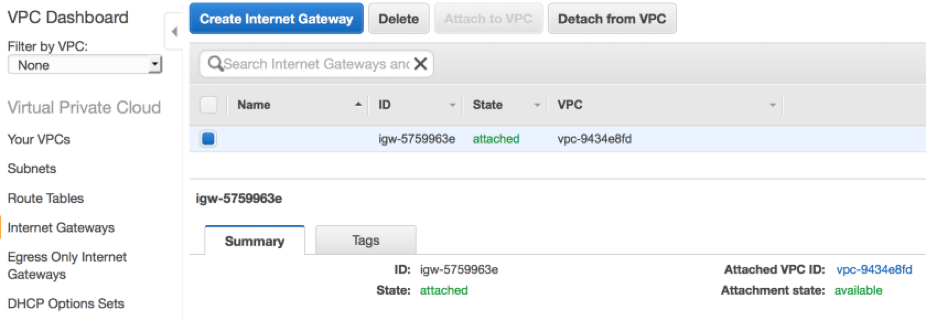
Routen-Tabelle
Im Zusammenhang mit dem Internet-Gateway habe ich bereits mehrfach das Routing erwähnt. Jede VPC ist mit einem impliziten Router verbunden. Dieser Router ist für den Benutzer nicht sichtbar und wird vollständig von AWS verwaltet und skaliert. Sichtbar ist die jedem Subnetz zugeordnete Routentabelle, die vom VPC-Router verwendet wird, um die zulässigen Routen für ausgehenden Netzwerkverkehr zu bestimmen, der ein Subnetz verlässt. Beachten Sie auf dem Screenshot unten, dass jede Routentabelle eine lokale Standardroute enthält, um die Kommunikation zwischen Instanzen in derselben VPC zu erleichtern, auch über Subnetze hinweg. Diese lokale Intra-VPC-Route ist implizit und kann nicht geändert werden. Im Falle der Hauptroutentabelle, die mit einem Standard-Subnetz verbunden ist, gibt es auch eine Route ins Internet über das Standard-Gateway für die VPC. 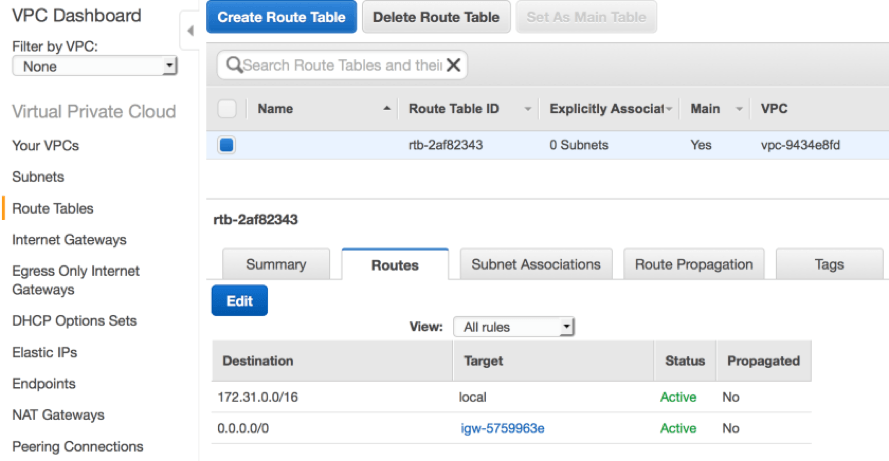 Beachten Sie auch, dass jedes Teilnetz mit einer Routentabelle verbunden sein muss. Wenn die Zuordnung nicht explizit definiert ist, wird ein Teilnetz implizit mit der Hauptroutentabelle verbunden.
Beachten Sie auch, dass jedes Teilnetz mit einer Routentabelle verbunden sein muss. Wenn die Zuordnung nicht explizit definiert ist, wird ein Teilnetz implizit mit der Hauptroutentabelle verbunden. 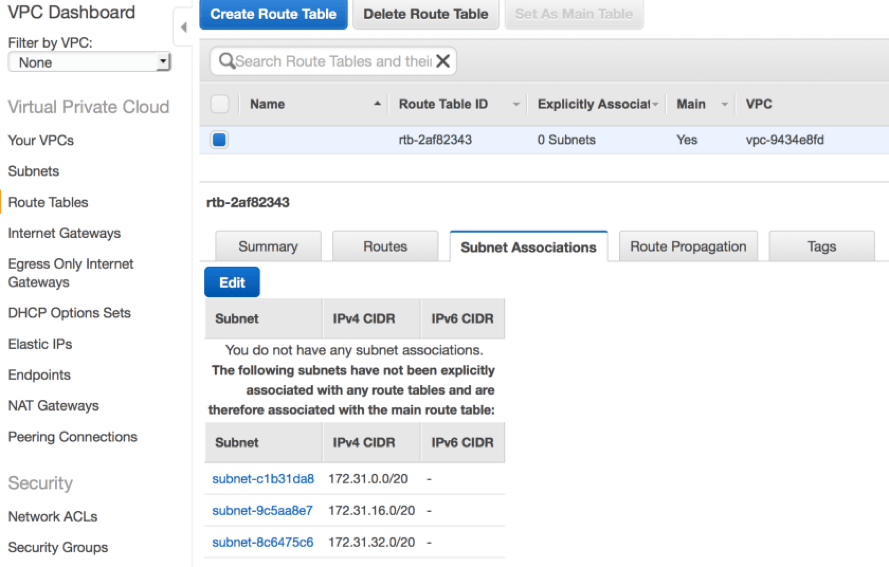
Netzwerksicherheit
Eine Sorge, die Sie vielleicht haben, ist die Netzwerksicherheit, insbesondere wenn alle Standard-Subnetze in einer Standard-VPC öffentlich und für den Internetverkehr offen sind. AWS bietet Sicherheitsmechanismen für Ihre Instanzen in Form von Netzwerk-ACLs und Sicherheitsgruppen. Diese beiden Mechanismen können zusammenwirken, um einen mehrschichtigen Schutz für Ihre EC2-Instanzen zu bieten. Eine ACL fungiert als Firewall, die den Netzwerkverkehr in und aus einem Subnetz kontrolliert. Sie erstellen Regeln, um Netzwerkverkehr für bestimmte Protokolle, über bestimmte Ports und für bestimmte IP-Adressbereiche zuzulassen oder abzulehnen. Netzwerk-ACLs sind zustandslos und haben getrennte Regeln für eingehende und ausgehende Verbindungen. Das bedeutet, dass sowohl eingehende als auch ausgehende Regeln erstellt werden müssen, um bestimmten Netzwerkverkehr in das Subnetz zu lassen und Antworten wieder durchzulassen. Jeder Regel wird eine Nummer zugewiesen, und alle Regeln werden beginnend mit der Regel mit der niedrigsten Nummer bewertet. Wenn der Verkehr auf die Firewall trifft, wird er anhand der Regeln in aufsteigender Reihenfolge ausgewertet. Sobald eine Regel ausgewertet wird, die auf den betrachteten Verkehr zutrifft, wird sie angewendet, unabhängig davon, was in einer nachfolgenden Regel angegeben ist. 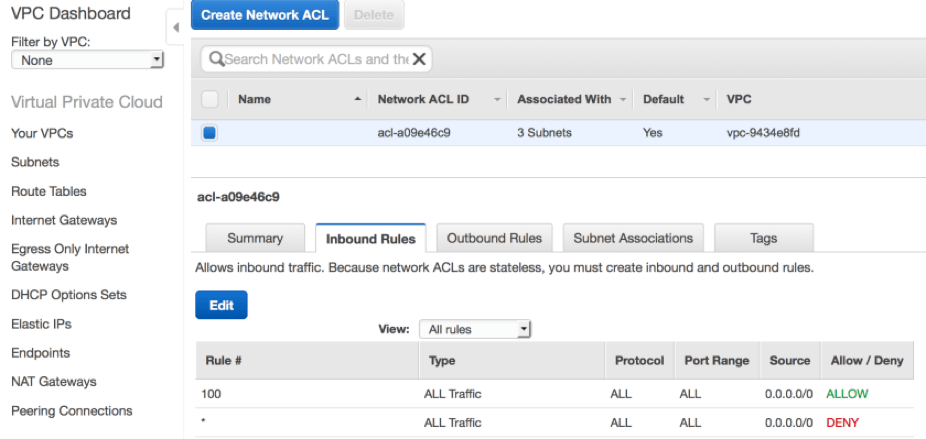
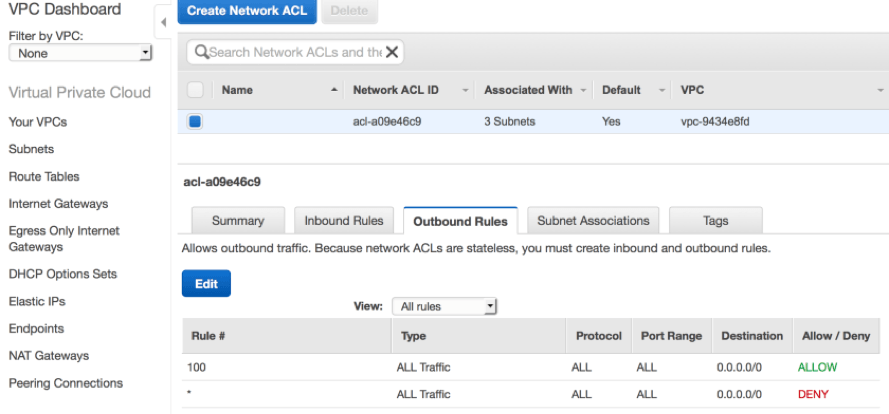 Wie bereits erwähnt, ist die Standard-ACL in einer Standard-VPC mit Regeln mit niedrigeren Nummern für eingehenden und ausgehenden Verkehr konfiguriert, die zusammen ausdrücklich bidirektionale Kommunikation für jedes Protokoll, über jeden Port und von und zu jeder Quelle oder jedem Ziel erlauben. Sie können eine ACL mit mehreren Subnetzen verknüpfen, aber ein einzelnes Subnetz kann nur mit einer ACL verknüpft werden. Wenn Sie eine ACL nicht speziell mit einem Subnetz verknüpfen, wird das Subnetz automatisch mit der Standard-ACL verknüpft. Dies ist der Fall bei Ihren Standard-VPCs, bei denen alle Subnetze mit der Standard-ACL verbunden sind.
Wie bereits erwähnt, ist die Standard-ACL in einer Standard-VPC mit Regeln mit niedrigeren Nummern für eingehenden und ausgehenden Verkehr konfiguriert, die zusammen ausdrücklich bidirektionale Kommunikation für jedes Protokoll, über jeden Port und von und zu jeder Quelle oder jedem Ziel erlauben. Sie können eine ACL mit mehreren Subnetzen verknüpfen, aber ein einzelnes Subnetz kann nur mit einer ACL verknüpft werden. Wenn Sie eine ACL nicht speziell mit einem Subnetz verknüpfen, wird das Subnetz automatisch mit der Standard-ACL verknüpft. Dies ist der Fall bei Ihren Standard-VPCs, bei denen alle Subnetze mit der Standard-ACL verbunden sind.
Sicherheitsgruppen
Sicherheitsgruppen werden als erste Verteidigungslinie betrachtet und bestehen aus einer Firewall, die auf Instanzebene angewendet wird. Das bedeutet, dass nur Instanzen, die explizit mit einer Sicherheitsgruppe verbunden sind, deren Regeln unterliegen, während alle Instanzen in einem Subnetz von der Netzwerk-ACL betroffen sind, die auf dieses Subnetz angewendet wird. Ähnlich wie bei ACLs erstellen Sie Regeln für ein- und ausgehenden Verkehr auf der Grundlage von Protokoll, Port und Quell- oder Ziel-IP. Es gibt jedoch einige Unterschiede:
- Sie können Regeln festlegen, um den Netzwerkverkehr zuzulassen, aber keine Regeln erstellen, um bestimmte Arten von Datenverkehr zu verweigern. Im Wesentlichen wird jeglicher Datenverkehr verweigert, mit Ausnahme des Datenverkehrs, den Sie ausdrücklich zulassen.
- Sicherheitsgruppen sind zustandsbehaftet, d. h. wenn Sie eine Regel erstellen, die eine bestimmte Art von Datenverkehr zulässt, wird als Antwort darauf auch der ausgehende Datenverkehr zugelassen, selbst wenn es keine ausdrückliche Regel gibt, die diesen Datenverkehr zulässt.
Jede Instanz muss mit einer Sicherheitsgruppe verknüpft werden. Wird beim Start keine Sicherheitsgruppe angegeben, wird die Instanz mit einer Standardsicherheitsgruppe verknüpft. 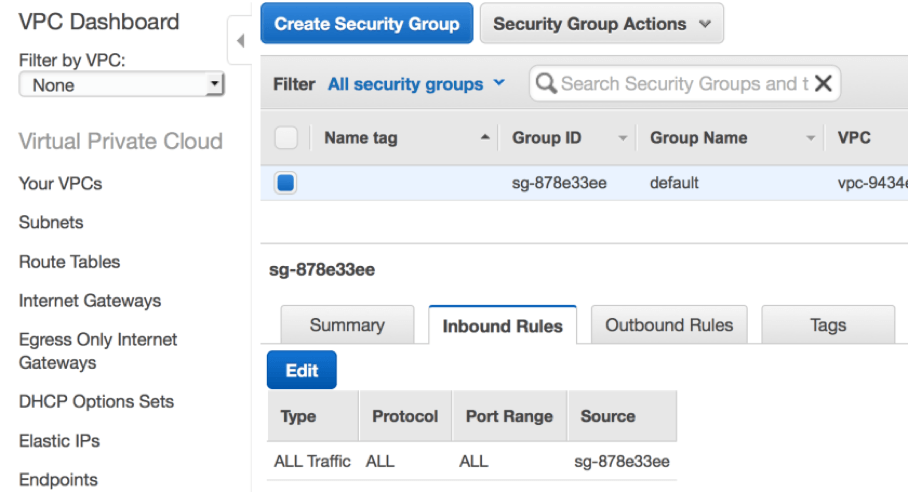 Aus der obigen Abbildung können Sie ersehen, dass eine Standardsicherheitsgruppe eine Regel hat, die nur eingehenden Verkehr von anderen Instanzen zulässt, die mit derselben Standardsicherheitsgruppe verbunden sind. Kein anderer eingehender Verkehr ist erlaubt.
Aus der obigen Abbildung können Sie ersehen, dass eine Standardsicherheitsgruppe eine Regel hat, die nur eingehenden Verkehr von anderen Instanzen zulässt, die mit derselben Standardsicherheitsgruppe verbunden sind. Kein anderer eingehender Verkehr ist erlaubt. 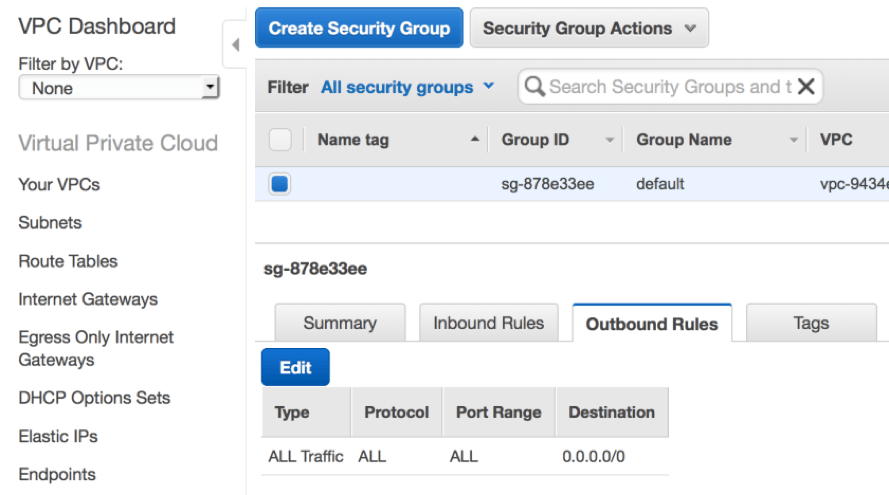 Betrachtet man die obigen ausgehenden Regeln, so wird der gesamte ausgehende Netzwerkverkehr von der Standardsicherheitsgruppe zugelassen. Dies gilt auch für den Datenverkehr in das Internet, da eine Standard-VPC eine Route zu einem Standard-Internet-Gateway hat. Die Standard-Sicherheitsgruppe kann zwar geändert werden, aber es wird nicht empfohlen, sie zu ändern. Rackspace empfiehlt stattdessen die Erstellung neuer Sicherheitsgruppen, die an Ressourcen angehängt werden können. Wie Sie sich vorstellen können, kann eine Standard-VPC für eine kleine, nicht kritische einstufige Anwendung geeignet sein, ist aber nicht ideal für eine stabile Produktionsumgebung. Aus diesem Grund ändern Benutzer oft ihre Standard-VPC-Konfigurationen, sobald sie sich mit der Technologie vertraut gemacht haben, und erstellen sogar benutzerdefinierte VPCs für den Produktionseinsatz. Bleiben Sie dran für meinen nächsten Blog-Beitrag, in dem wir genau das tun und einen häufigen Anwendungsfall mit einer benutzerdefinierten VPC mit einer öffentlichen Subnetzebene und einer privaten Subnetzebene aufschlüsseln werden. Besuchen Sie Rackspace , um weitere Informationen über unsere AWS-zertifizierten Experten und die Möglichkeiten zu erhalten, wie sie Kunden bei der Nutzung von AWS helfen.
Betrachtet man die obigen ausgehenden Regeln, so wird der gesamte ausgehende Netzwerkverkehr von der Standardsicherheitsgruppe zugelassen. Dies gilt auch für den Datenverkehr in das Internet, da eine Standard-VPC eine Route zu einem Standard-Internet-Gateway hat. Die Standard-Sicherheitsgruppe kann zwar geändert werden, aber es wird nicht empfohlen, sie zu ändern. Rackspace empfiehlt stattdessen die Erstellung neuer Sicherheitsgruppen, die an Ressourcen angehängt werden können. Wie Sie sich vorstellen können, kann eine Standard-VPC für eine kleine, nicht kritische einstufige Anwendung geeignet sein, ist aber nicht ideal für eine stabile Produktionsumgebung. Aus diesem Grund ändern Benutzer oft ihre Standard-VPC-Konfigurationen, sobald sie sich mit der Technologie vertraut gemacht haben, und erstellen sogar benutzerdefinierte VPCs für den Produktionseinsatz. Bleiben Sie dran für meinen nächsten Blog-Beitrag, in dem wir genau das tun und einen häufigen Anwendungsfall mit einer benutzerdefinierten VPC mit einer öffentlichen Subnetzebene und einer privaten Subnetzebene aufschlüsseln werden. Besuchen Sie Rackspace , um weitere Informationen über unsere AWS-zertifizierten Experten und die Möglichkeiten zu erhalten, wie sie Kunden bei der Nutzung von AWS helfen.
Tags:





